CLOUD SECURITY SERVICES
Every entity that holds personal information for individuals has a high responsibility to protect that data. Since the internet first took off, incoming threats from the cloud have been a known enemy and should never be taken lightly. As attacks continue to grow stronger, simple anti-virus or log aggregation systems are no longer a dependable service; they allow too much unseen activity through to enterprises network.
You need a cloud security service that will not only detect all dangerous activity but notify you as soon as the threat enters the company’s network. While there are plenty of edge devices that seem to be trustworthy, they are often not good enough. A reliable SIEM solution is going to give you what you need for cloud security.
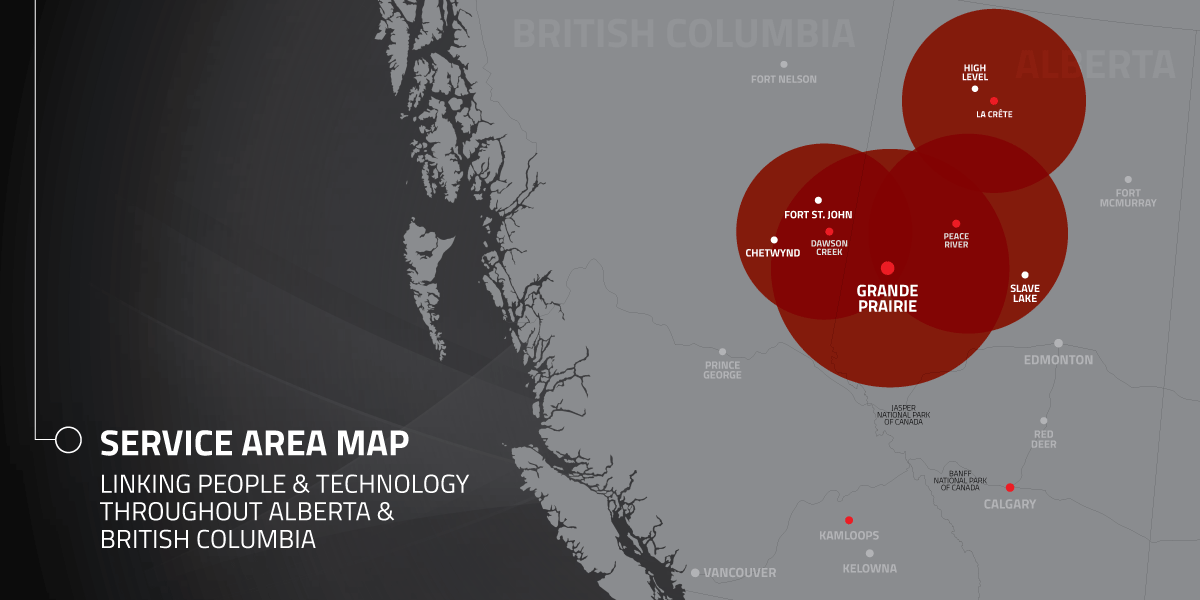
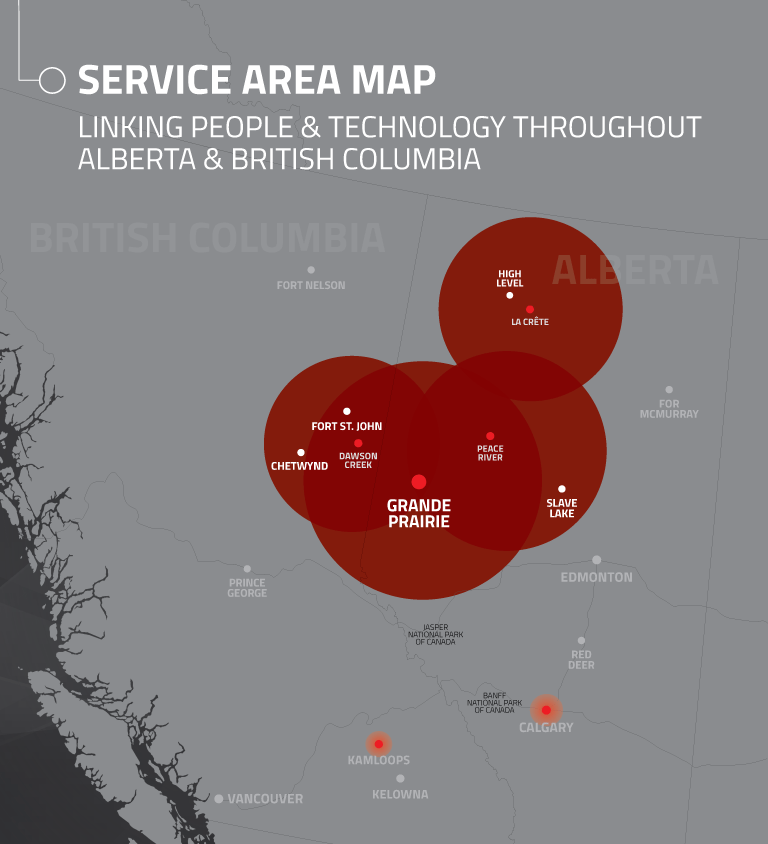
How can you be sure that the information that is being stored in the cloud is safe? You simply find a service that can monitor any critical system no matter where they are located.
The SIEM platform we use can be applied to either your client’s site and managed remotely as SIEM Management, or we can host it in the cloud as SIEMaaS.
When a company stores its information in the cloud, how are they supposed to know when a threat produces or where it is coming from? There are a lot of encryption codes and security measures taken, but these precautions can be bypassed by files being accessed by a large number of individuals or by being moved, replicated and shared frequently. Faulting equipment, bugs, and erroneous actions can also create an opening for online hackers. With a SIEM, a company’s online environment is monitored and will be aware of any threats.
With full visibility on the company’s cloud activity, we are able to notify MSPs within minutes of a threat entering the cloud. Further, you have a team of experts that understand what the threat is and how to resolve the situation. Our team gives MSPs specific instructions on what needs to be done in order to keep the environment safe.
Just as SIEM Management works, SIEMaaS works efficiently in the cloud by covering multiple hosts at once. Data breaches, data loss, account hijacking, and system and application vulnerabilities are some of the threats that come from the cloud, and it is in your best interest to have a credible team of specialists on your side to recognize hacker credentials.
If you have more specific questions about cloud security or our services, call one of our company representatives.